Wow nice find
Lemmy
Everything about Lemmy; bugs, gripes, praises, and advocacy.
For discussion about the lemmy.ml instance, go to !meta@lemmy.ml.
You should probably open an issue on the lemmy-ui repository :)
I think this is a backend error, with my poor Rust reading skills I arrived to this find_by_email_or_name function where I believe the problem is: https://github.com/LemmyNet/lemmy/blob/f24999027e26fc77cc3808674f4f37fb1883c20f/crates/db_views/src/local_user_view.rs#L85
It uses ilike which in SQL should allow things like % and _ to be used as placeholders for matching any character(s): https://www.postgresql.org/docs/14/functions-matching.html#FUNCTIONS-LIKE
Nice find, I'll create a PR to fix this.
Sorry to bother you again, it took me some time to find this again on GitHub. This login bug I was experiencing was introduced when fixing this other login bug, you can see in that commit that eq was changed to ilike but now your new pull request reintroduces that old bug with the case-sensitiveness of the usernames during login. I think the solution to both bugs would be converting to uppercase before comparing with eq (and having a computed uppercased column indexed on the database). I don't know enough Rust to propose code changes or send a pull request, I hope my description of the solution is good enough for someone more knowledgeable to write the code.
We did originally want to force usernames to be lowercase (to prevent confusing name conflicts, but haven't forced any DB constraints on that yet, only for the actor_id column it looks like). For now due to the security implications, it makes sense to use eq instead of ilike.
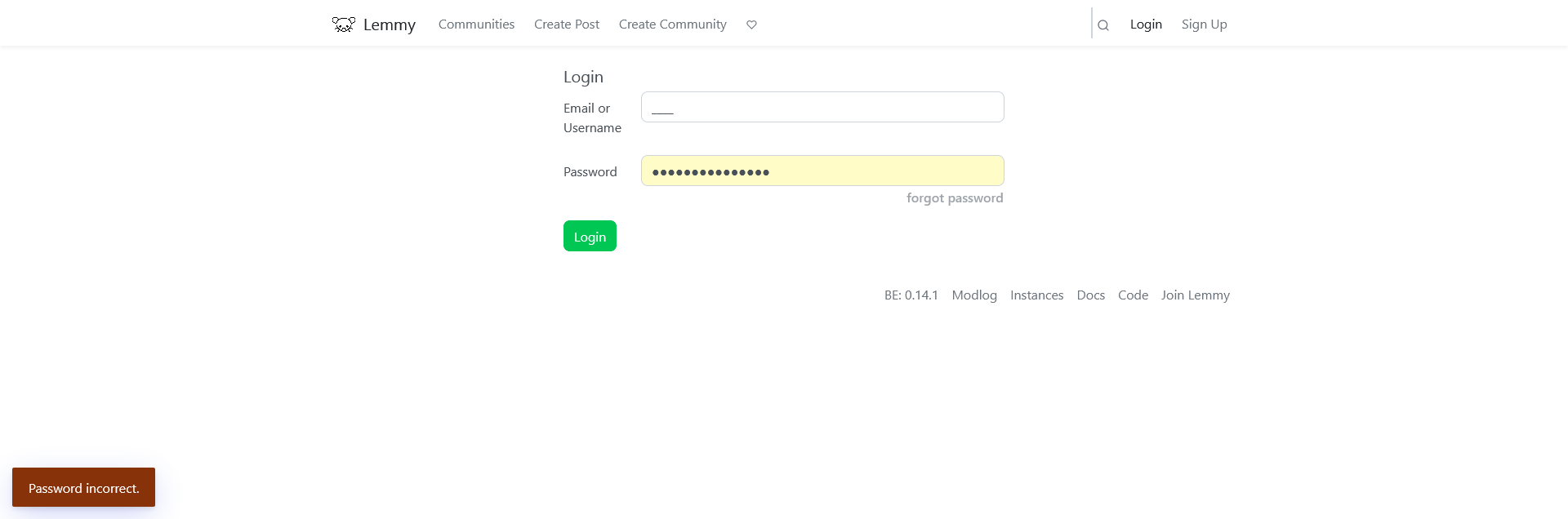
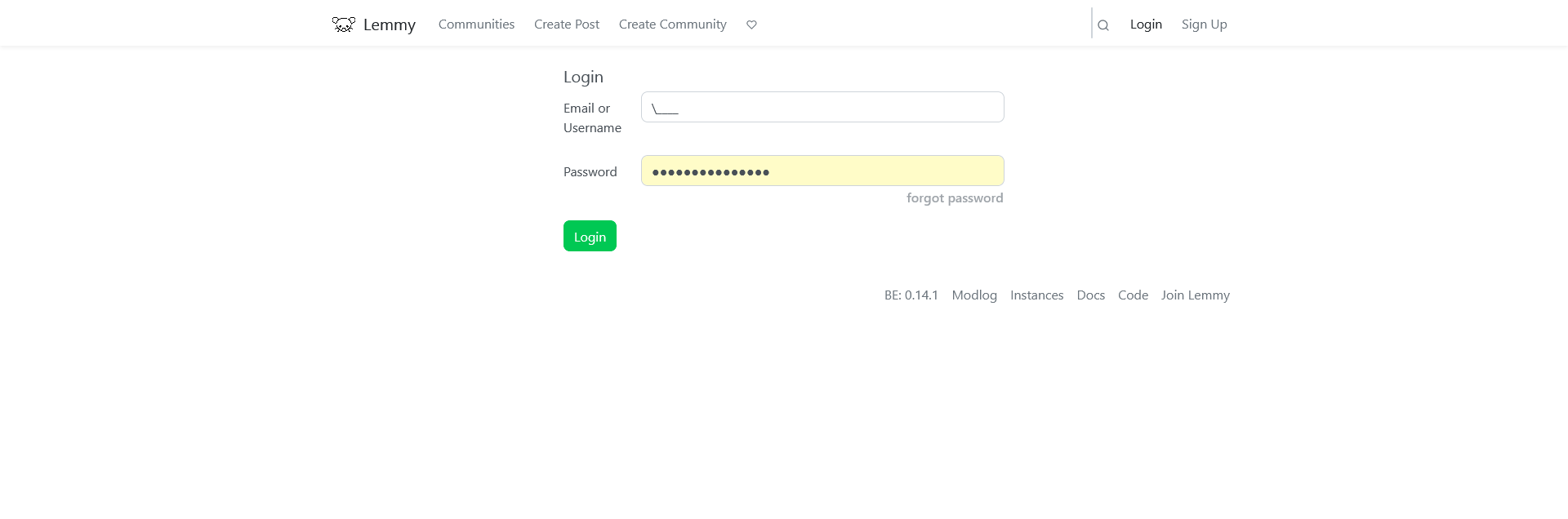
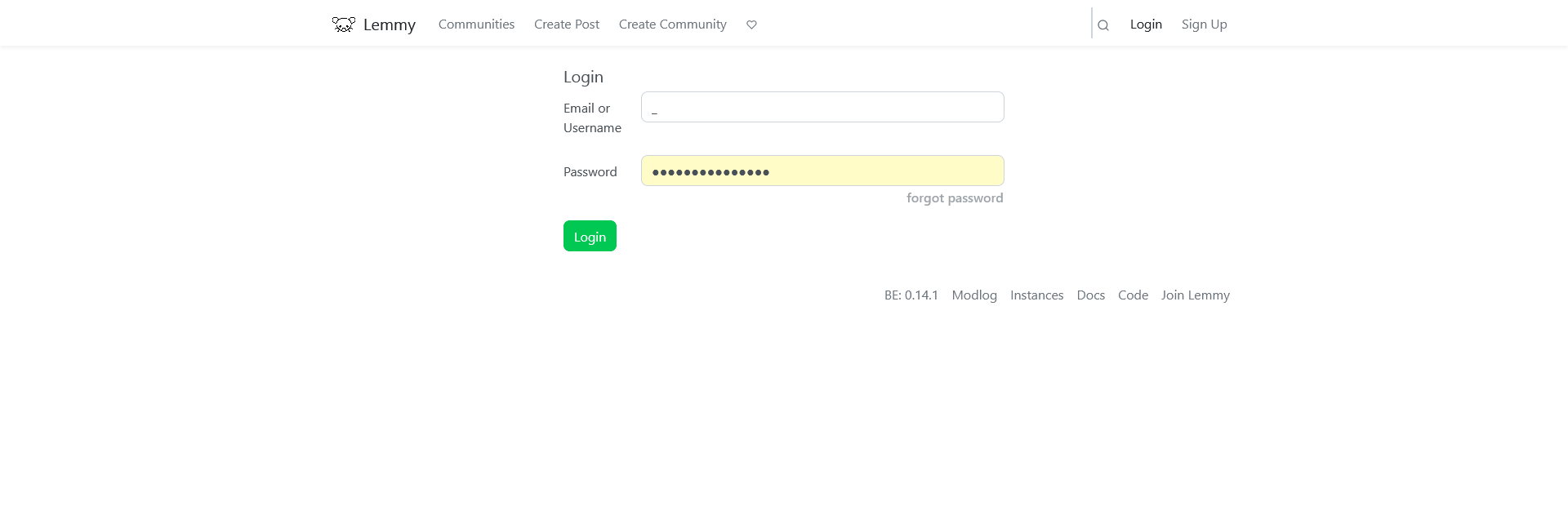
So does this mean it's possible to access any account that you know the password of if the wildcards are used for the username?
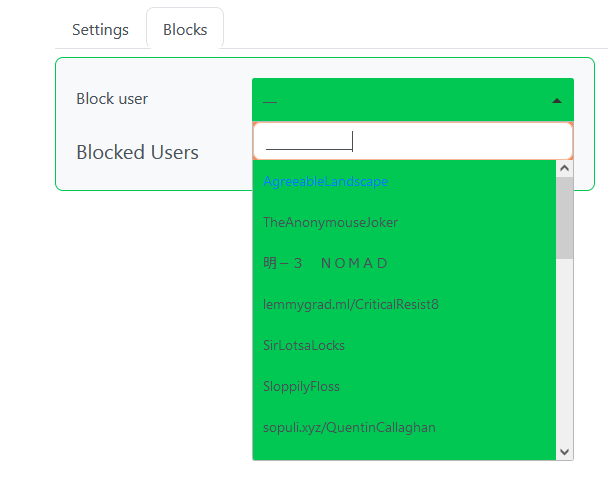
You need to know the exact length of the account name (it seems that % is filtered because it is not allowed in usernames and only underscores can be used as placeholders). The risk is minimal, the only possible exploit that comes to mind is trying a list of compromised/common passwords and testing each with underscore usernames of different lengths. That way you will be able to log in as the first person (by database query sort order) using a compromised/common password whose username (or email) has the same amount of characters as underscores you tried. So the usual advice applies: don't use a compromised or common password and you will be safe, use a password manager and let it generate a random password for you if you can. Also this is easy to detect server side and if there is any kind of rate limiting the attack won't work, I wouldn't worry about this bug.
Great find!
Thanks!