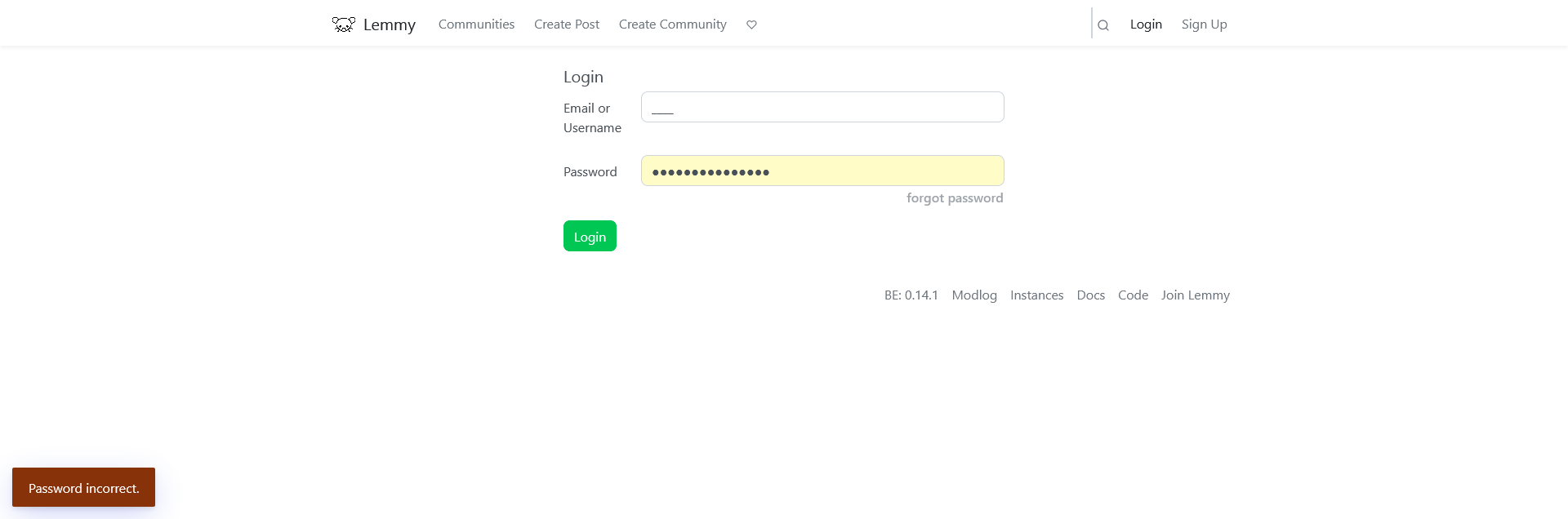
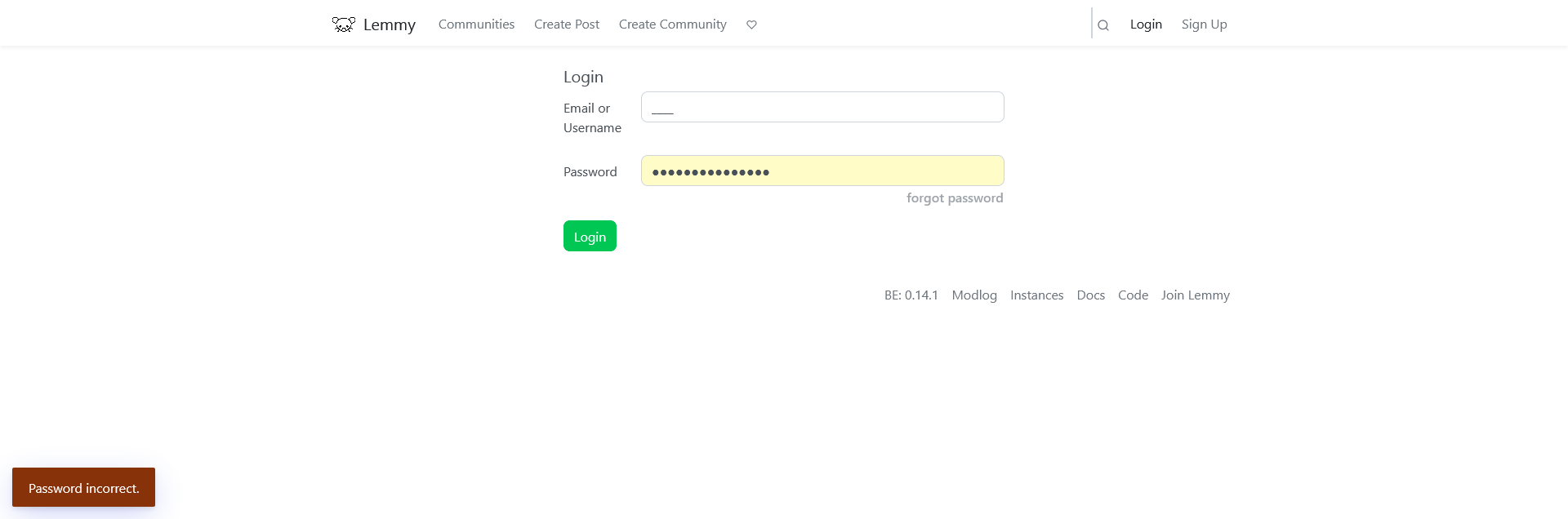
Trying to log in using my username ____ doesn't work, it displays this error (this bug has existed since I created the account):
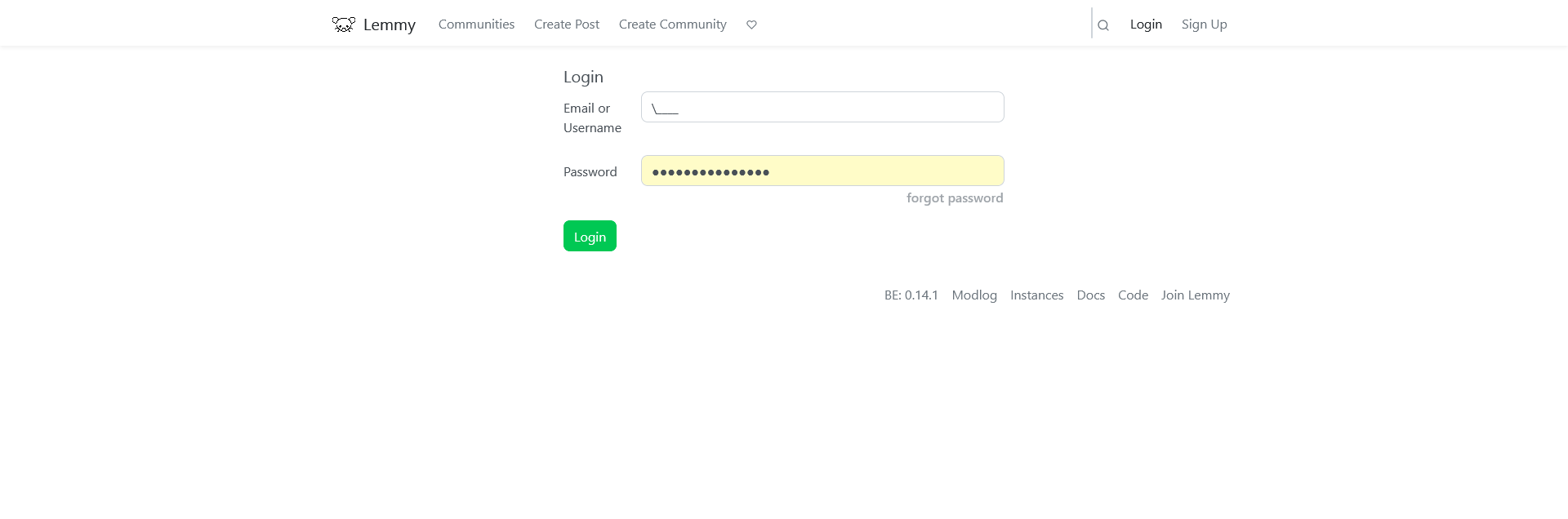
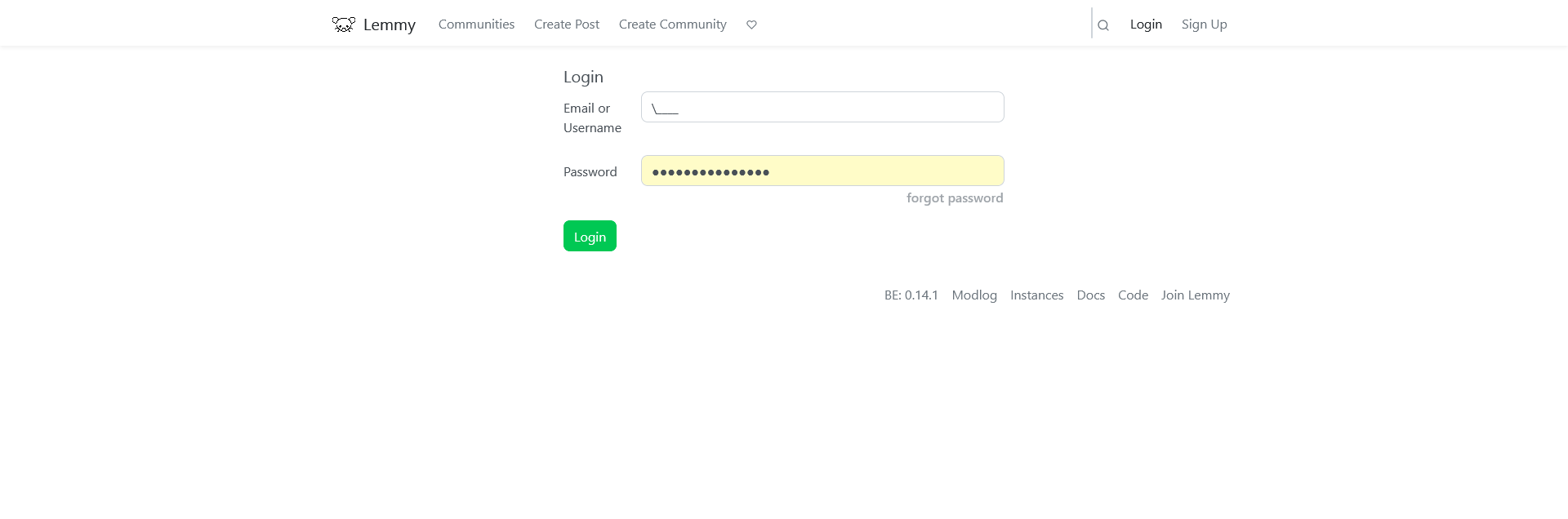
Today I discovered a workaround, I can log in if I prepend a \ to my username:
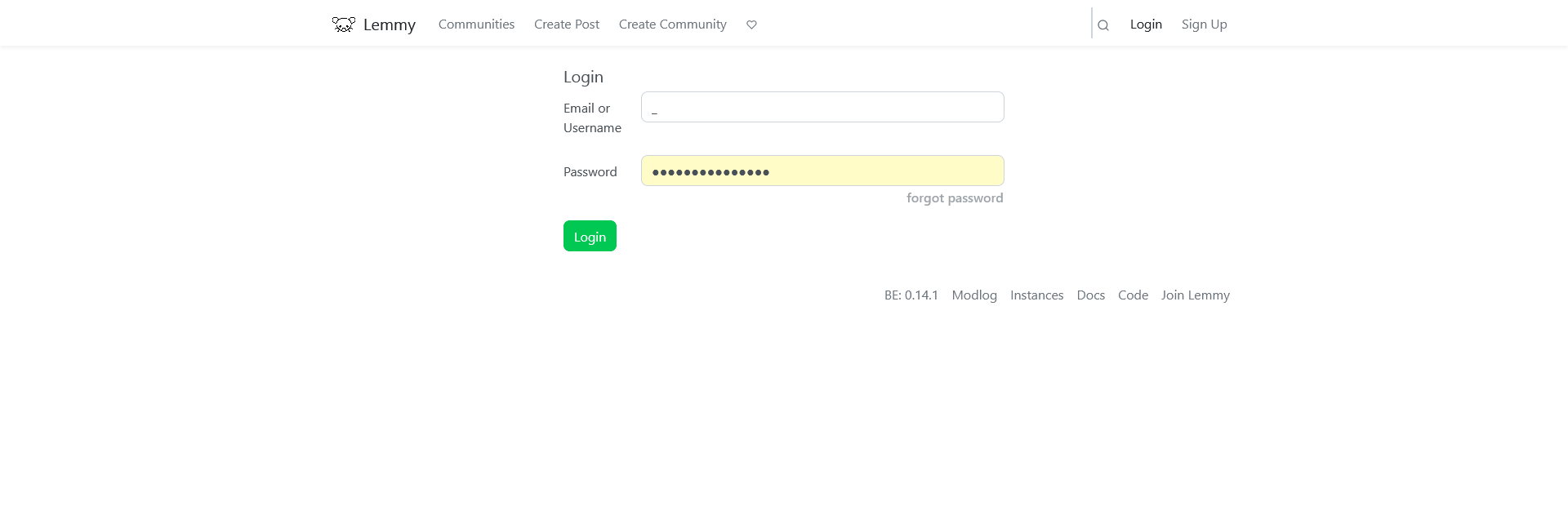
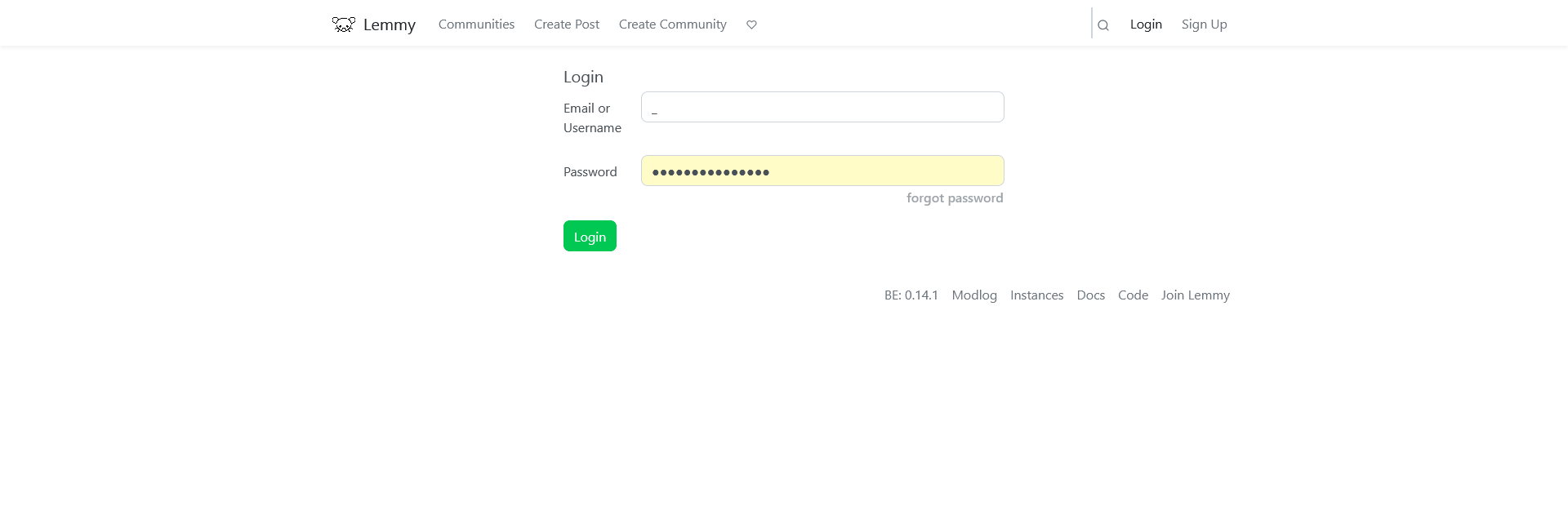
It also works if I write my username like this \_\_\_\_
Using a single _ for the username (and removing the minlength of 3 of the field with the html inspector) logs me in too, but not into this account, I get logged in into my @Lee account that has the same password:
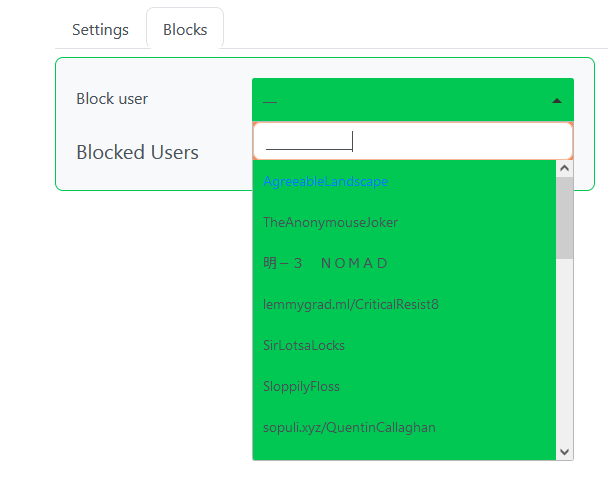
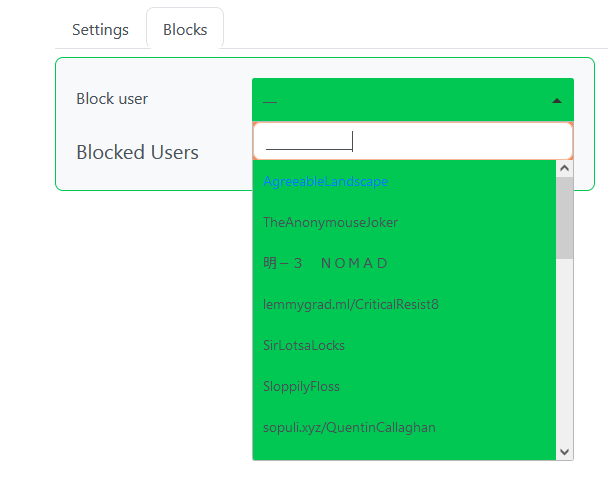
I haven't read the code (I don't think I can, I never managed to learn Rust) but my theory is that _ is being used as a placeholder or matchall value when comparing usernames and emails. If I escape it with \ it works because it matches my username. If I write a single unescaped _ it logs me into my other account because the email of that account is set to a single character "@" which should match a single matchall underscore.
Edit: the autocomplete field in the block users page seems to confirm my theory as it matches any username as long or longer than the number of underscores I write:
So does this mean it's possible to access any account that you know the password of if the wildcards are used for the username?
You need to know the exact length of the account name (it seems that % is filtered because it is not allowed in usernames and only underscores can be used as placeholders). The risk is minimal, the only possible exploit that comes to mind is trying a list of compromised/common passwords and testing each with underscore usernames of different lengths. That way you will be able to log in as the first person (by database query sort order) using a compromised/common password whose username (or email) has the same amount of characters as underscores you tried. So the usual advice applies: don't use a compromised or common password and you will be safe, use a password manager and let it generate a random password for you if you can. Also this is easy to detect server side and if there is any kind of rate limiting the attack won't work, I wouldn't worry about this bug.
Great find!
Thanks!