this post was submitted on 24 Jul 2023
815 points (98.0% liked)
Programmer Humor
32536 readers
626 users here now
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
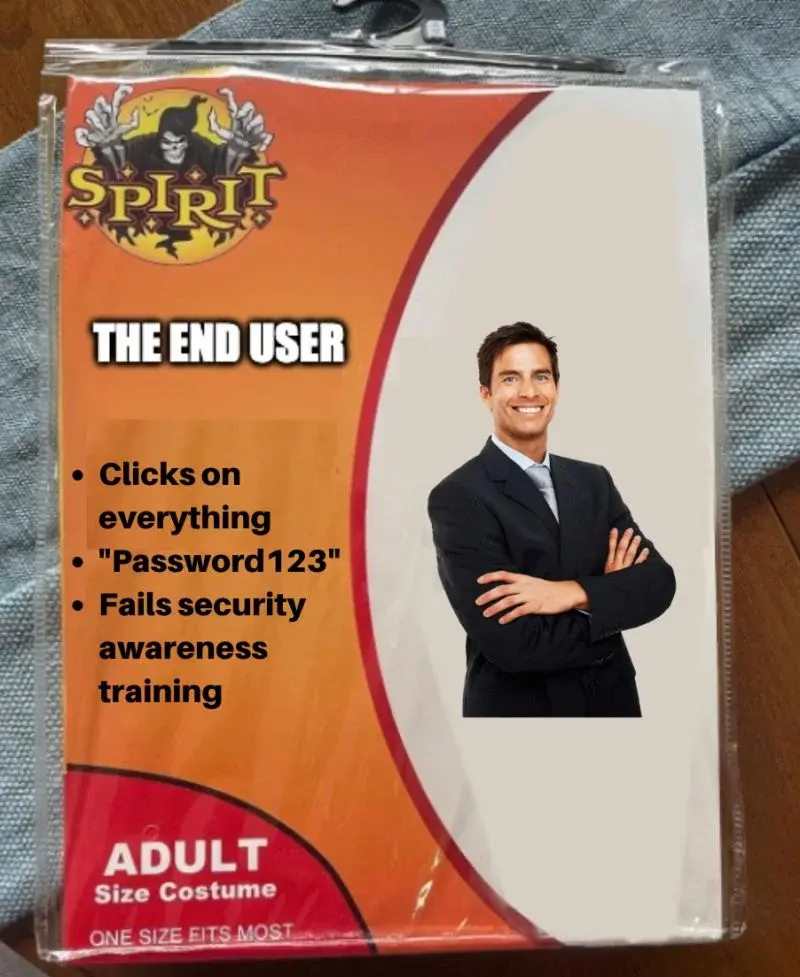
Password expiration is no longer considered a best practice. FYI.
I got to step 20, where my password suddenly caught on fire and Paul died.
My day is ruined.
expired
expired
Yes, that's true, and hasn't been considered so for a long time
It was never best practices for anyone who had common sense.
It just forced people to make insecure, easy to remember passwords, cause they were gonna be changed in again soon so why make it complicated and hard to remember.
I know I do this. Add another exclamation mark.
Psh... That's amateur, I just keep incrementing the number at the end 'password1', 'password2', etc. Gotta fool the password reuse counter!
why so?
Encourages users to just add a rotating number or other not too secure thing to their password. I know that’s what I did when I worked somewhere with that dumbfuck policy.
Yep. My least secure password is the one I use at work because I'm restricted to 9-12 characters, can't be sequential forwards or backwards including keys next to each other (abc, 123, qwerty), can't begin with a number, must contain at least three numbers, must be at least four characters different from your last twelve passwords, and must be changed every 90 days. Oh and it can't include your first or last name.
Most of my coworkers just use a family members name and then change a few numbers at the end and keep a post it note at their desk with the numbers so they don't forget it.
Oh really? How come?
NIST removed password expiration from their recommendations in 2020. Instead they recommend only forcing password changes when compromise is suspected.
The main argument is that they do not make users or systems demonstrably safer and encourage bad password habits.
I would imagine most users change their password by only 1 character, and maybe even in sequential order.
When time comes to change the password, it becomes password1234 instead of password123. Or password234. Something easy to remember, most users don't care about best security practices, and changing to a similar password is very convenient. Especially if it's "only" for work stuff
The original idea was that you would take how long it took to brute-force a password, then require the password be changed before that. But we have better hashing now, like bcrypt, where you can tune it so that brute forcing anything would take 100s of years.