I've been using this image with different providers for years. I would highly recommend it.
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
I wrote a bash script this that updates cloudflare using their API if the public has changed, and just have it running with crontab.
It's been running for 6 years now without issue so I recommend this
Same but powershell. Works like a charm runs every 5 minutes
I was using that same docker image for a while but somewhat recently migrated to this: https://github.com/favonia/cloudflare-ddns
It handles 5 of my domains all from the single container. Highly recommend it!
This is what I use as well.
You might want to check out their Tunnels product. It might do what you want and is easy.
I've seen it mentioned in a bunch of videos and articles, but I didn't like the idea of Cloudflare scanning all the stuff that is transferred from and to my server. If I opt just for their DNS service and update it through the API they can't do that, right?
No, then they only handle your DNS setup, which is still okay in my eyes.
Its certainly far away from scanning all HTTP traffic. Not to forget the juicy metadata they get about the users across a big chunk of the internet, perfect tracking machine in a neat package with easy access by the government.
cloudflare is an intelligence company who's flagship product involves them mitming your TLS.
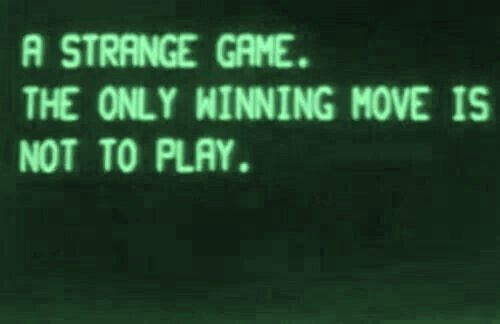
why bother self-hosting, if you do it from behind cloudflare?
Because it provides an extra layer of protection at no cost and makes DNS management very convenient, as well as other free features.
Convenience will kill the cat
That's why I didn't want to use Cloudflare Tunnels, but just Dynamic DNS. I though that they had access to the stuff you transfer only if you use their tunneling feature and for the reasons you said is something I would prefer to avoid.
The thing is that I bought my domain on Infomaniak and most of the self-hosting tutorials I've seen recommend Cloudflare. Would you suggest something different?
EDIT: I just realized that ddclient (that I was already considering to set up ddns with cloudflare) also supports Infomaniak directly! (I don’t know how before making this post I didn’t saw it 😅) So I’ll probably go for that way in order to cut out Cloudflare from the equation and rely on one external company less. Thank you :)
Because I don’t want to expose my home IP.
@cypherpunks
@cypherpunks @rhys mitming?
cloudflare's service puts them in the middle - so, HTTPS doesn't encrypt traffic between the browser and your server anymore, but instead between the browser and CF, and then (separately) between CF and your server. CF is an antidote to intelligence agencies' problem of losing visibility when most of the web switched to HTTPS a decade ago.
CF is an antidote to intelligence agencies' problem of losing visibility when most of the web switched to HTTPS a decade ago.
This is a claim that will need evidence backing it up.
Here is what I used before I switched to desec.io: https://gist.github.com/haansn08/50565768c66c5fbf382b2bc2484e8a41
All those do is essentially call the Cloudflare API. They'll all work reasonably well. The linked Docker image for example is essentially doing the bulk of it in this bash script which they call from a cron and some other container init logic which I imagine is to do the initial update when the container starts.
Pick whatever is easiest and makes most sense for you. Even the archived Docker thing is so simple, I wouldn't worry about it being unmaintained because it can reasonably be called a finished product. It'll work until Cloudflare upgrades their API and shuts down the old one, which you'd get months to years of warning because of enterprise customers.
Personally, that's a trivial enough task I'd probably just custom-write a Python script to call their API. They even have a python library for their API. Probably like 50-100 lines long tops. I have my own DNS server and my DDNS "server" is a 25 lines PHP script, and the client is a curl command in a cronjob.
DDNS is a long solved and done problem. All the development is essentially just adding new providers.
but I haven’t find that much information on which labels should I add to set it up.
I’ve not automated creation of records for new services, but I’ve made it easier for myself by making hostname.domain.ext the dynamic DNS (managed by a simple cron job with curl commands interacting with the API), and all service.domain.ext just CNAME to the main record.
I don’t think I’ll be automating the creation of the CNAME records because something tells me I’d end up leaving a bunch of dead service DNS records behind.
I think that this could be the cleanest solution, could you share the curl command you used to interact with the API? (Of course replacing your actual access token with ** etc.)
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I've seen in this thread:
| Fewer Letters | More Letters |
|---|---|
| CF | CloudFlare |
| DNS | Domain Name Service/System |
| HTTP | Hypertext Transfer Protocol, the Web |
| HTTPS | HTTP over SSL |
| IP | Internet Protocol |
| SSL | Secure Sockets Layer, for transparent encryption |
| TLS | Transport Layer Security, supersedes SSL |
5 acronyms in this thread; the most compressed thread commented on today has 7 acronyms.
[Thread #373 for this sub, first seen 25th Dec 2023, 05:15] [FAQ] [Full list] [Contact] [Source code]