Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
You seem to understand neither security nor privacy.
I get to give you access to all my photos so that you can just proxy calls to my server?
Just share your own damn server people, this "I'm behind 7 proxies" bs is getting tiring.
You‘re supposed to host this yourself.
This thing reduces the attack surface of the inmich installation.
If it is good, or bad or fitting to your security model can only be said by you. But honestly it sounds like a sensible thing to do
And it adds its own "attack surface".
And? It lowers the attack surface of Immich. Attack surface is about the surface, whatever an attacker can use to get leverage. This acts as an intermediate between Immich and a public viewer, controlling how a threat actor can access a private Immich server. It helps reduce external attack surface while increasing overall system complexity. Since the project is small, it is easy to audit the code.
It's some rando's project that has existed for "nearly a month", has no community, is unlikely to have any rapid response to any issues, and probably won't be supported for more than a year.
But sure - go ahead and run it for "security purposes".
You can "reduce surface area" by simply putting in place nginx or apache (real supported software) and blacklisting the endpoints you don't like.
I like to judge software based on its actually merit and not on the theoretical possibility it is vulnerable. It very well could be vulnerable, but without auditing it we are just speculating, which in the real world means nothing. Every project starts somewhere, without community, followers, and "5 years of support". I am not saying I would trust this software in a security critical situation, just that your speculation means nothing.
This is literally the entire justification for the project. It's assuming theoretical vulnerabilities in Immich.
Which is the point of this software (security critical situation).
This project has zero community support. That's not speculative, it's a fact. "Every project starts somewhere" is just a tautology that means nothing. Every project that fails starts somewhere.
It's all about the risk matrix. The theoretical likelihood of a vulnerability in Immich might be low, but the severity of that risk is catastrophic in terms of personal data leaking.
The likelihood of a risk in this proxy might be medium or even high according to you, but the severity is low. It doesn't have access to any of your personal data. All it does is talk to Immich via Immich's public sharing API.
One of the contributors to this project is bo0tzz, who is one of the maintainers of Immich.
It might be zero. It's "unknown" (according to me I guess).
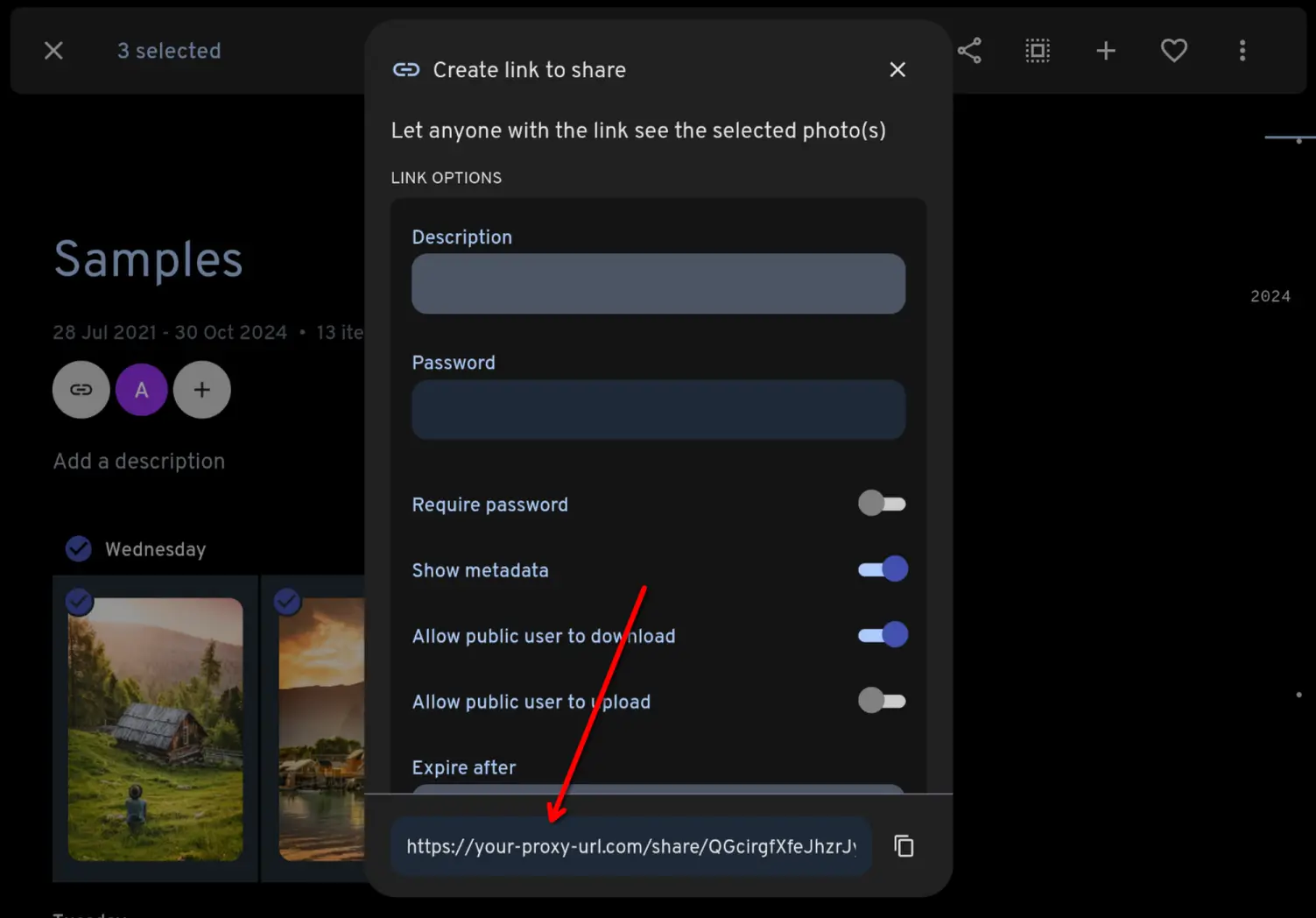
I've dug into the code a bit out of curiosity - it seems to me that "proxy" is a misnomer. It's a stripped-down "view" layer built on top of the API. But has the same endpoints as the main immich app for shared things so that you can create links that work with it so it kinda looks like a proxy. But it's just a "simplified public view" of sorts.
Meh.