this post was submitted on 06 Sep 2024
201 points (99.5% liked)
Linux
48965 readers
1898 users here now
From Wikipedia, the free encyclopedia
Linux is a family of open source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991 by Linus Torvalds. Linux is typically packaged in a Linux distribution (or distro for short).
Distributions include the Linux kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name GNU/Linux to emphasize the importance of GNU software, causing some controversy.
Rules
- Posts must be relevant to operating systems running the Linux kernel. GNU/Linux or otherwise.
- No misinformation
- No NSFW content
- No hate speech, bigotry, etc
Related Communities
Community icon by Alpár-Etele Méder, licensed under CC BY 3.0
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Sorry to be that guy, but this sounds like a cybersecurity nightmare. While everybody was busy to come up with schemes that make absolutely sure that only trusted sources can update a system to avoid having malicious players push their code to users, this one just takes any rando's pile of whatever and injects it straight into the system's core? Like, that doesn't sound like a good idea.
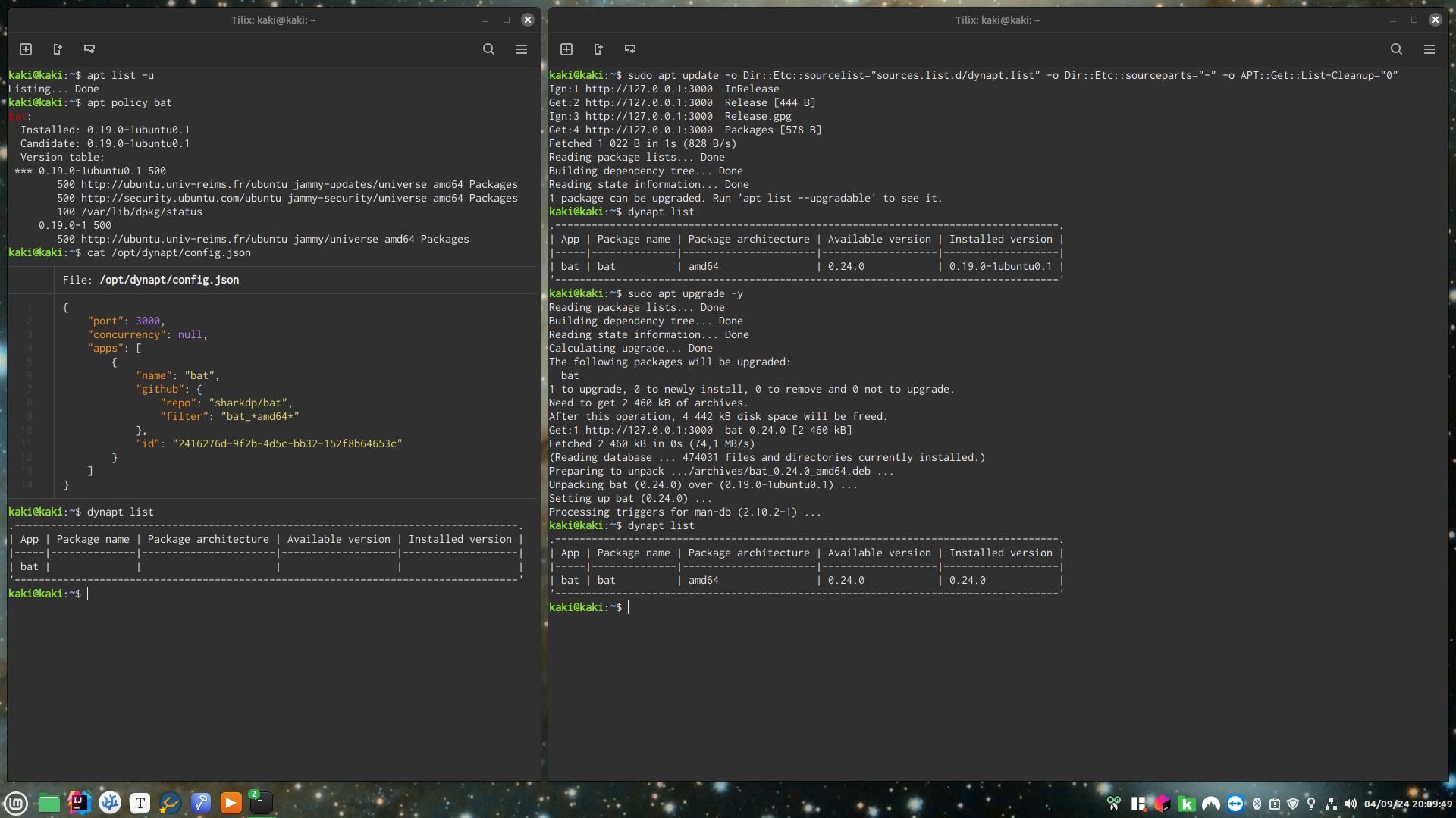
Well, I'm just automating what people currently have to do manually : visit GitHub and download DEB and install DEB.
If the automated process would be dangerous then the manual process also would be, and that would be on the maintainer for not providing an APT repository or a Flatpak, not on the user for just downloading from GitHub.
It’s a cool concept, but automation breeds laziness (by design, to an extent) and lazy end users tend to shoot themselves in the foot. So it isn’t great for security, but it also isn’t that much worse for security :)
Since some people with money tend to be litigious, and, of course, I am not a lawyer, I would advise a warning message (or part of the license if you don’t want to muck up your CLI), if you don’t have one, to force the user to accept and acknowledge that the software they are installing using this tool is not verified to be safe.
How is the manual step more secure though ?
What does the user do before downloading a DEB that makes that gap between manual and automated ?
I'd be willing to try and reproduce that, but I don't see anything.
I didn’t say it was more secure, I said it’s about the same.
The difference is a person being forced to go to a website to download software means more steps and more time to consider the safety of what they’re doing. It’s part psychological.
Not all such packages are retrieved from GitHub, I remember downloading numerous .deb files direct over the past 25 years (even as recent as downloading Discord manually some years back).
The main point I’m making is that you should legally protect yourself, it’s a low and reasonable effort.
You said automation breeds laziness (by design, to an extent) and lazy end users tend to shoot themselves in the foot.
So, my question is : what part of automating download of DEBs from a specific source can be shooting oneself in the foot compared to doing the same thing manually every time ?
The MIT license will take care of that.
Also, to force the user to accept and acknowledge that the software they are installing using this tool is not verified to be safe is inducing fear and/or guilt, therefore is bad UX, I'm not doing that.
I already answered that first question.
And then all those app store fronts that say whether a flatpak is verified or not is inducing fear and/or guilt and is therefore bad UX. It's not, but you are free to have your opinion.
Have fun then, I'm done wasting my time here.
Yeah. You should never do that. Like ever. Build from source; or use a vendored tarball. https://wiki.debian.org/DontBreakDebian
.deb is a terribly insecure nightmare thats held up by the excellent debian packagers, gpg , and checksums, and stable release model. don't use .deb files.
I'm and end user working for end users.
Yeah, we all are. What's your point?
End users are also developers. All computer users are developers. You are developing.
By making a script that lets me get backdoors and shitty packages with ease? The linux package distribution system is a nightmare, Debian is the least bad approach. There is basically always a better option to using a .deb file. If you come across something that isn't packaged, I recommend Flatpak, building from source (and installing unprivileged), or using the developers vendored tarball (installing unprivileged).
https://wiki.debian.org/SecureApt
By using local .debs you lose the benefit of:
My point is that I'm working a solution for end users.
The solutions you're offering are not user-friendly.
I see it more as a local repo. Like, setup the repo to do what you would have done manually so that you don't have to do it on multiple computers. I could be misunderstanding it though.
You understand perfectly.
No matter where you install from, you have to trust the source. Indeed, you have to trust every step in the supply chain.
If you are getting your code straight from the author, you are eliminating an exploit that’s introduced by a compromised account of a packager.
Carry on.
Which is not what you are doing at all with a .deb file. A .deb file is a binary with a bunch of scripts to "properly" install your package. Building from source is what you SHOULD be doing. Debian has an entire policy handbook on how packages are supposed to be packaged. Progrmatically you can review the quality of a package with 'lintian'. .debs made by developers following a wiki tutorial can't even come close. remember, apt installs happen as root and can execute arbitrary code.
Also, debian packagers can be project maintainers, so they can be "the author."