this post was submitted on 29 Jun 2023
45 points (100.0% liked)
Technology
37711 readers
369 users here now
A nice place to discuss rumors, happenings, innovations, and challenges in the technology sphere. We also welcome discussions on the intersections of technology and society. If it’s technological news or discussion of technology, it probably belongs here.
Remember the overriding ethos on Beehaw: Be(e) Nice. Each user you encounter here is a person, and should be treated with kindness (even if they’re wrong, or use a Linux distro you don’t like). Personal attacks will not be tolerated.
Subcommunities on Beehaw:
This community's icon was made by Aaron Schneider, under the CC-BY-NC-SA 4.0 license.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Is this, by any chance, originated from the sub called
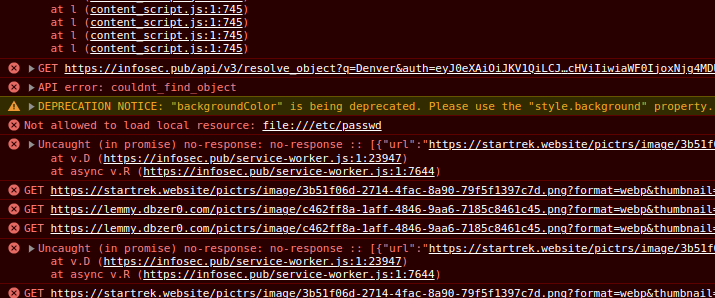
ignore me? In that case is probably my bad because is set as the image of the channel. I was playing with lemmy in the previous version and forgot about it, sorry.That alert appears because your browser is trying to load an image with that path, nothing dangerous or remotely exploitable, don't worry.
Edit: I removed it so you shouldn't see the alert anymore.
P.S. not, it's not trying to steal anything, it's your browser trying to load that file as an image but instead of being let's say this url:
https://beehaw.org/pictrs/image/c0e83ceb-b7e5-41b4-9b76-bfd152dd8d00.png(this sub icon) , it's this onefile:///etc/passwdso you browser is doing the request to your own file. Don't worry, nothing got compromised./cc @shellsharks@infosec.pub>
But... why? Why even put that URL there? Even if it was most likely harmless for all users, this still looks like an attempt at data exfiltration.
Because I wanted to try if others URI schemas were supported instead of http / https. file:// was a valid one. Don't worry, the day an attempt of data exfil will happen, you will not see it though your console logs.